
How Encryption Keeps Your Files Safe Online
Every time you send an email, back up a photo to the cloud, or share a confidential document online, your data travels through countless servers and networks. Without protection, that data can easily be intercepted or misused by cybercriminals. This is where encryption steps in—the invisible shield guarding your digital life.
Encryption has become one of the most crucial components of data security and online privacy. It ensures that sensitive information—from personal photos to business contracts—remains secure even if it falls into the wrong hands. Understanding how encryption works and how to keep encrypted files safe can help individuals and businesses strengthen their data encryption and security strategies.
In this guide, we’ll break down what encryption is, how it protects your files online, and the best practices for keeping your encrypted data secure, with practical insights into tools like SendMega, a trusted platform
What Is Encryption, and Why Does It Matter?
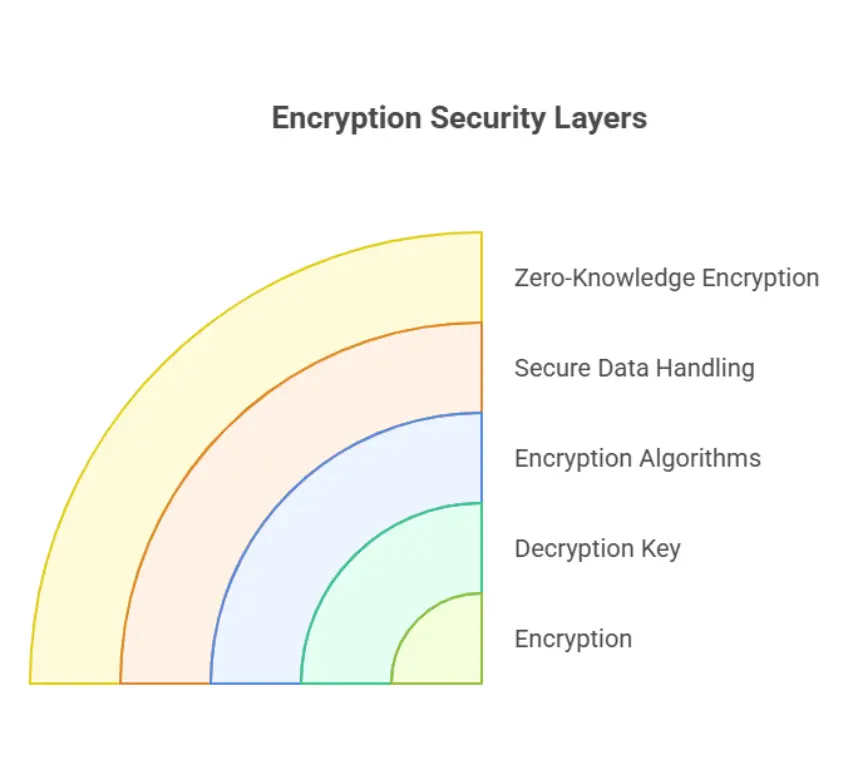
At its core, encryption is the process of converting readable data (known as plaintext) into an unreadable form (ciphertext). Only authorized parties with the correct decryption key can unlock and read the original information.
For instance, when you use a secure platform like SendMega, Google Drive, or Mega.io, your files are encrypted before they even leave your device. That means even if a hacker intercepts them, the data appear as random, unreadable characters—virtually impossible to decode without the proper key.
Encryption isn’t just about privacy; it’s a critical layer of defense against the growing risks of cyberattacks, data theft, and surveillance. In a world where breaches make daily headlines, data encryption technology is the foundation of modern cybersecurity.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
The Science Behind Encryption: How It Works
Encryption relies on mathematical algorithms to scramble data into a coded format. There are two primary types of encryption used in today’s digital systems:
Symmetric Encryption:
In symmetric encryption, the same key is used to encrypt and decrypt data. It’s fast and efficient, making it ideal for large-scale file storage or secure file transfer. The most common standard, AES (Advanced Encryption Standard), is used by major tech companies and government agencies worldwide.
Asymmetric Encryption:
Asymmetric encryption uses two keys—a public key for encryption and a private key for decryption. This method is used in secure emails, digital signatures, and end-to-end encrypted communication. It ensures that even if someone accesses the public key, they still can’t decrypt the data without the private one.
Many advanced platforms, including Google Drive, SendMega, and Mega.io, combine both methods (AES and RSA) to deliver multi-layered protection—ensuring your files are safe during both storage and transmission.
In symmetric encryption, the same key is used to encrypt and decrypt data. It’s fast and efficient, making it ideal for large-scale file storage or secure file transfer. The most common standard, AES (Advanced Encryption Standard), is used by major tech companies and government agencies worldwide.
Asymmetric Encryption:
Asymmetric encryption uses two keys—a public key for encryption and a private key for decryption. This method is used in secure emails, digital signatures, and end-to-end encrypted communication. It ensures that even if someone accesses the public key, they still can’t decrypt the data without the private one.
Many advanced platforms, including Google Drive, SendMega, and Mega.io, combine both methods (AES and RSA) to deliver multi-layered protection—ensuring your files are safe during both storage and transmission.
Asymmetric encryption uses two keys—a public key for encryption and a private key for decryption. This method is used in secure emails, digital signatures, and end-to-end encrypted communication. It ensures that even if someone accesses the public key, they still can’t decrypt the data without the private one.
Many advanced platforms, including Google Drive, SendMega, and Mega.io, combine both methods (AES and RSA) to deliver multi-layered protection—ensuring your files are safe during both storage and transmission.
Why Keeping Encrypted Files Safe Still Matters
While encryption protects your data, it’s not foolproof if the keys or passwords are poorly managed. The real power of encryption lies not only in the algorithms but in how securely you store, handle, and transfer your encrypted data.
Even encrypted files can become vulnerable if:
- The decryption keys are lost or exposed.
- Weak passwords are used.
- Files are stored on unprotected devices.
- Cloud storage lacks proper cybersecurity and encryption safeguards.
That’s why platforms like SendMega are designed with built-in zero-knowledge encryption—meaning not even the service provider can access your files. Only you (and those you authorize) can decrypt the data.
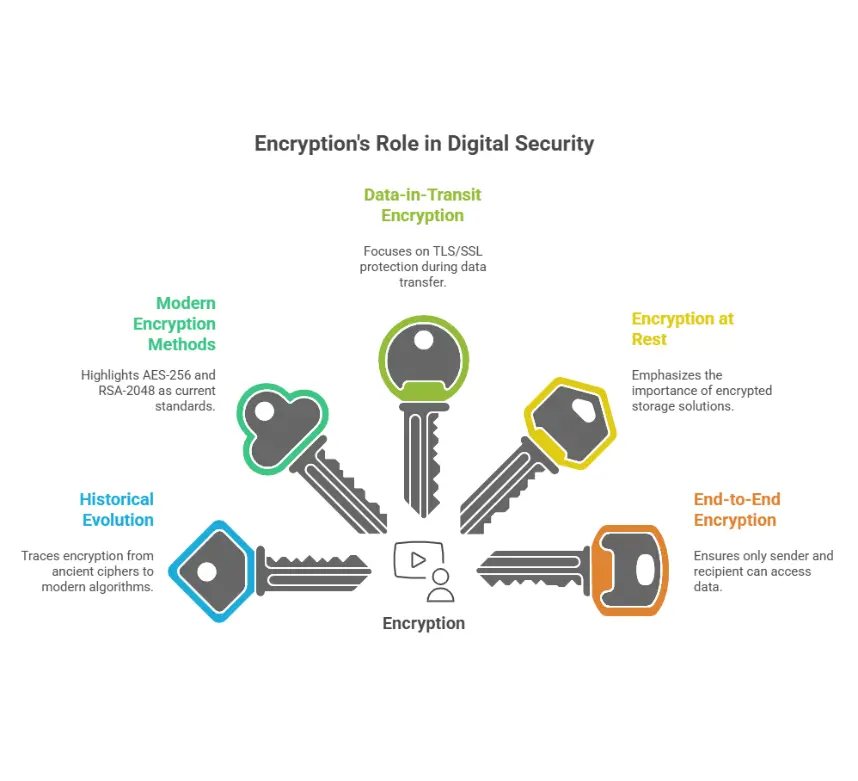
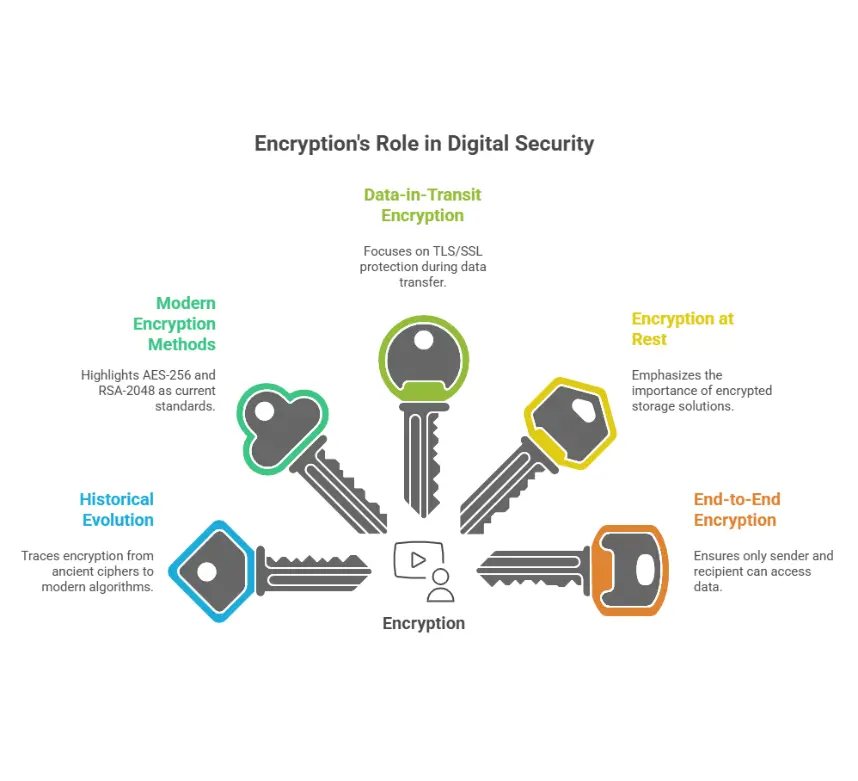
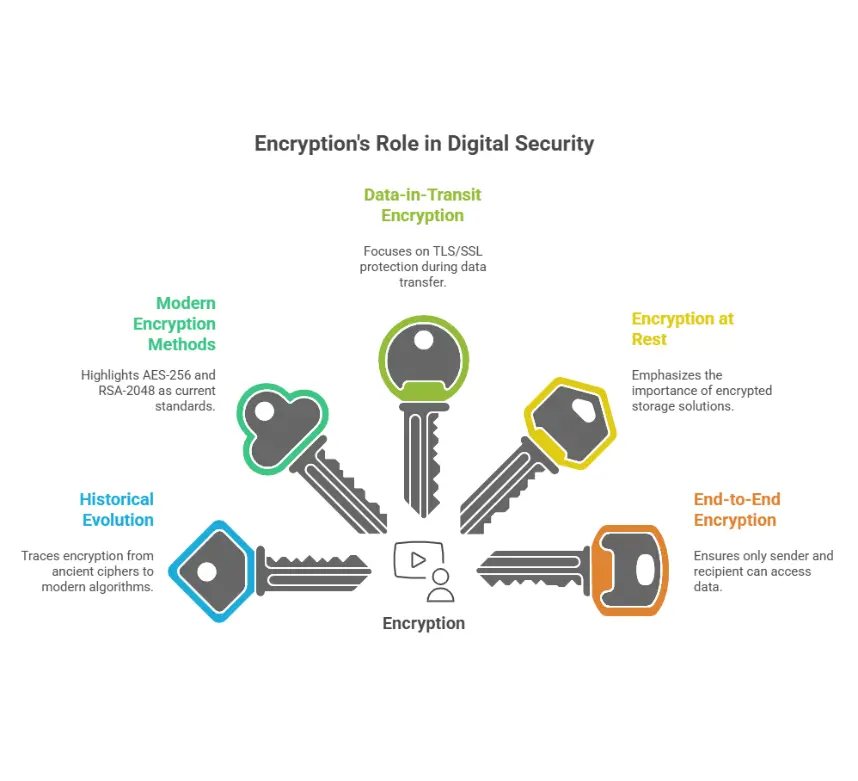
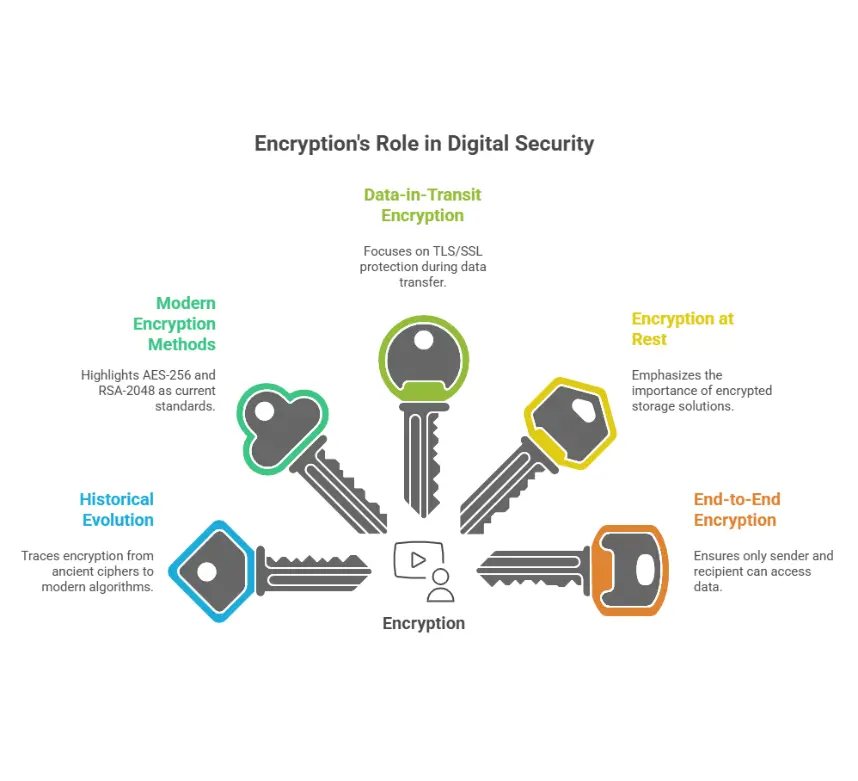
A Brief History of Encryption
Encryption is far from a modern concept. It dates back thousands of years — from the simple Caesar cipher used by the Romans to the complex Enigma machine used during World War II.
In the digital age, encryption has evolved from military communication tools to the backbone of data security and encryption on the internet. Today, it protects everything from your online banking to your secure encrypted emails and cloud backups.
Modern encryption methods like AES-256 and RSA-2048 are now considered virtually unbreakable, even with advanced computing power. But as technology progresses, so do the threats—making constant innovation in data encryption technology essential.
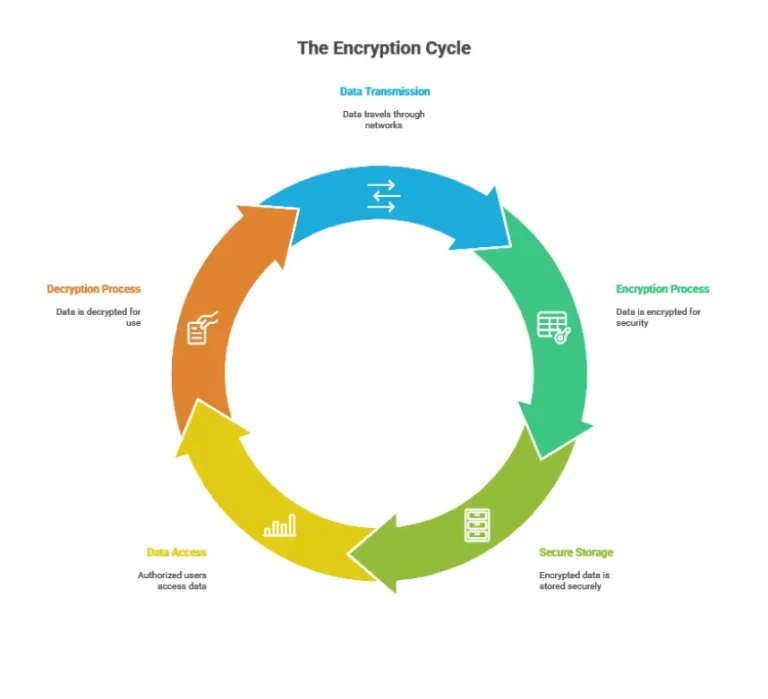
How Encryption Protects Your Files Online
When you upload or share files online, there are multiple stages where your data could be exposed—during transfer, while stored on servers, or through unauthorized access. Encryption ensures protection at every stage.
Here’s how it works:
Encryption During Transfer
When files are sent from your device to another system (e.g., via email or cloud upload), TLS/SSL encryption protects data while in motion. This process is called data-in-transit encryption.
Encryption at Rest
Files stored on your device, server, or cloud are encrypted to prevent access even if storage is compromised. SendMega, for example, uses advanced encrypted cloud storage to keep files protected at rest.
End-to-End Encryption
End-to-end encryption ensures that only the sender and recipient can decrypt the data. Even service providers or intermediaries can’t access your files, ensuring true privacy and secure file storage.
When files are sent from your device to another system (e.g., via email or cloud upload), TLS/SSL encryption protects data while in motion. This process is called data-in-transit encryption.
Encryption at Rest
Files stored on your device, server, or cloud are encrypted to prevent access even if storage is compromised. SendMega, for example, uses advanced encrypted cloud storage to keep files protected at rest.
End-to-End Encryption
End-to-end encryption ensures that only the sender and recipient can decrypt the data. Even service providers or intermediaries can’t access your files, ensuring true privacy and secure file storage.
Files stored on your device, server, or cloud are encrypted to prevent access even if storage is compromised. SendMega, for example, uses advanced encrypted cloud storage to keep files protected at rest.
End-to-End Encryption
End-to-end encryption ensures that only the sender and recipient can decrypt the data. Even service providers or intermediaries can’t access your files, ensuring true privacy and secure file storage.
End-to-end encryption ensures that only the sender and recipient can decrypt the data. Even service providers or intermediaries can’t access your files, ensuring true privacy and secure file storage.
Best Practices for Keeping Encrypted Files Safe
Encrypting your files is just the first step. Maintaining their safety requires following a few essential best practices:
Use Strong Encryption Standards
Always choose software or platforms that use robust encryption algorithms like AES-256 or RSA-2048.
Keep Your Encryption Keys Secure
Treat your decryption keys like the keys to your home—store them offline, in password managers, or with hardware security modules.
Enable Multi-Factor Authentication (MFA)
Add an extra layer of protection to prevent unauthorized access even if a password is compromised.
Update Your Software Regularly
Outdated encryption software can contain vulnerabilities. Always install updates to stay protected against emerging threats.
Avoid Storing Encrypted Files on Public Devices
Public computers or unsecured Wi-Fi networks can expose your data. Stick to private networks and trusted cloud encryption services like SendMega.
Backup Your Encrypted Files Safely
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
The Role of Encryption in Secure File Sharing
In today’s collaborative digital environment, teams and individuals share files across devices, countries, and networks. But file sharing without encryption exposes sensitive information to potential threats.
This is where encrypted file sharing becomes essential. Platforms like SendMega, Google Drive, and Mega.io use end-to-end encryption and zero-knowledge storage, ensuring that only the sender and intended recipient can access the data.
Whether you’re transferring confidential business documents or sharing personal media, encrypted cloud storage ensures:
-
Data integrity (no unauthorized changes)
-
Confidentiality (no one else can view it)
-
Accessibility (available anywhere, anytime)
Emerging Trends and the Future of Encryption
The future of encryption is exciting—and challenging. As quantum computing and AI-driven cybersecurity evolve, so will encryption technologies.
Post-Quantum Encryption:
Quantum computers could eventually break today’s strongest encryption. Researchers are already developing post-quantum encryption methods that can resist these advanced attacks.
Homomorphic Encryption:
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Security Risks to Watch For
Even with strong encryption in place, certain vulnerabilities can still compromise data security.
Being aware of these risks is essential for maintaining a strong defense.
-
Weak Passwords
Passwords that are easy to guess or crack can undermine even the strongest encryption.
-
Phishing Attacks
Attackers may trick users into revealing encryption keys or login credentials.
-
Poor Encryption Management
Reusing outdated algorithms or failing to rotate keys weakens overall security.
-
Human Error
Storing passwords in plain text or misconfiguring systems can expose sensitive data.
Combating these threats requires awareness, strong cybersecurity practices, and reliable tools. Choosing a trusted service like SendMega helps reduce these vulnerabilities by combining encryption with secure infrastructure and privacy-focused design.
Final Thoughts
Encryption is not just a technical process—it’s a mindset. In a world where data breaches and cyber threats are ever-present, knowing how encryption keeps your files safe online empowers you to protect what matters most.
From understanding how to encrypt your data to using secure encrypted email and cloud encryption security, every step contributes to a safer digital environment. SendMega, Google Drive, mega.io, and other similar platforms bring that protection to your everyday workflow—combining encryption, privacy, and ease of use.
In the end, the key to secure online life isn’t just encryption—it’s awareness, consistency, and trusted technology. Protect your data, choose encrypted solutions, and take charge of your digital world.
Always choose software or platforms that use robust encryption algorithms like AES-256 or RSA-2048.
Keep Your Encryption Keys Secure
Treat your decryption keys like the keys to your home—store them offline, in password managers, or with hardware security modules.
Enable Multi-Factor Authentication (MFA)
Add an extra layer of protection to prevent unauthorized access even if a password is compromised.
Update Your Software Regularly
Outdated encryption software can contain vulnerabilities. Always install updates to stay protected against emerging threats.
Avoid Storing Encrypted Files on Public Devices
Public computers or unsecured Wi-Fi networks can expose your data. Stick to private networks and trusted cloud encryption services like SendMega.
Backup Your Encrypted Files Safely
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
The Role of Encryption in Secure File Sharing
In today’s collaborative digital environment, teams and individuals share files across devices, countries, and networks. But file sharing without encryption exposes sensitive information to potential threats.
This is where encrypted file sharing becomes essential. Platforms like SendMega, Google Drive, and Mega.io use end-to-end encryption and zero-knowledge storage, ensuring that only the sender and intended recipient can access the data.
Whether you’re transferring confidential business documents or sharing personal media, encrypted cloud storage ensures:
-
Data integrity (no unauthorized changes)
-
Confidentiality (no one else can view it)
-
Accessibility (available anywhere, anytime)
Emerging Trends and the Future of Encryption
The future of encryption is exciting—and challenging. As quantum computing and AI-driven cybersecurity evolve, so will encryption technologies.
Post-Quantum Encryption:
Quantum computers could eventually break today’s strongest encryption. Researchers are already developing post-quantum encryption methods that can resist these advanced attacks.
Homomorphic Encryption:
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Security Risks to Watch For
Even with strong encryption in place, certain vulnerabilities can still compromise data security.
Being aware of these risks is essential for maintaining a strong defense.
-
Weak Passwords
Passwords that are easy to guess or crack can undermine even the strongest encryption.
-
Phishing Attacks
Attackers may trick users into revealing encryption keys or login credentials.
-
Poor Encryption Management
Reusing outdated algorithms or failing to rotate keys weakens overall security.
-
Human Error
Storing passwords in plain text or misconfiguring systems can expose sensitive data.
Combating these threats requires awareness, strong cybersecurity practices, and reliable tools. Choosing a trusted service like SendMega helps reduce these vulnerabilities by combining encryption with secure infrastructure and privacy-focused design.
Final Thoughts
Encryption is not just a technical process—it’s a mindset. In a world where data breaches and cyber threats are ever-present, knowing how encryption keeps your files safe online empowers you to protect what matters most.
From understanding how to encrypt your data to using secure encrypted email and cloud encryption security, every step contributes to a safer digital environment. SendMega, Google Drive, mega.io, and other similar platforms bring that protection to your everyday workflow—combining encryption, privacy, and ease of use.
In the end, the key to secure online life isn’t just encryption—it’s awareness, consistency, and trusted technology. Protect your data, choose encrypted solutions, and take charge of your digital world.
Treat your decryption keys like the keys to your home—store them offline, in password managers, or with hardware security modules.
Enable Multi-Factor Authentication (MFA)
Add an extra layer of protection to prevent unauthorized access even if a password is compromised.
Update Your Software Regularly
Outdated encryption software can contain vulnerabilities. Always install updates to stay protected against emerging threats.
Avoid Storing Encrypted Files on Public Devices
Public computers or unsecured Wi-Fi networks can expose your data. Stick to private networks and trusted cloud encryption services like SendMega.
Backup Your Encrypted Files Safely
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
The Role of Encryption in Secure File Sharing
In today’s collaborative digital environment, teams and individuals share files across devices, countries, and networks. But file sharing without encryption exposes sensitive information to potential threats.
This is where encrypted file sharing becomes essential. Platforms like SendMega, Google Drive, and Mega.io use end-to-end encryption and zero-knowledge storage, ensuring that only the sender and intended recipient can access the data.
Whether you’re transferring confidential business documents or sharing personal media, encrypted cloud storage ensures:
-
Data integrity (no unauthorized changes)
-
Confidentiality (no one else can view it)
-
Accessibility (available anywhere, anytime)
Emerging Trends and the Future of Encryption
The future of encryption is exciting—and challenging. As quantum computing and AI-driven cybersecurity evolve, so will encryption technologies.
Post-Quantum Encryption:
Quantum computers could eventually break today’s strongest encryption. Researchers are already developing post-quantum encryption methods that can resist these advanced attacks.
Homomorphic Encryption:
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Security Risks to Watch For
Even with strong encryption in place, certain vulnerabilities can still compromise data security.
Being aware of these risks is essential for maintaining a strong defense.
-
Weak Passwords
Passwords that are easy to guess or crack can undermine even the strongest encryption.
-
Phishing Attacks
Attackers may trick users into revealing encryption keys or login credentials.
-
Poor Encryption Management
Reusing outdated algorithms or failing to rotate keys weakens overall security.
-
Human Error
Storing passwords in plain text or misconfiguring systems can expose sensitive data.
Combating these threats requires awareness, strong cybersecurity practices, and reliable tools. Choosing a trusted service like SendMega helps reduce these vulnerabilities by combining encryption with secure infrastructure and privacy-focused design.
Final Thoughts
Encryption is not just a technical process—it’s a mindset. In a world where data breaches and cyber threats are ever-present, knowing how encryption keeps your files safe online empowers you to protect what matters most.
From understanding how to encrypt your data to using secure encrypted email and cloud encryption security, every step contributes to a safer digital environment. SendMega, Google Drive, mega.io, and other similar platforms bring that protection to your everyday workflow—combining encryption, privacy, and ease of use.
In the end, the key to secure online life isn’t just encryption—it’s awareness, consistency, and trusted technology. Protect your data, choose encrypted solutions, and take charge of your digital world.
Add an extra layer of protection to prevent unauthorized access even if a password is compromised.
Update Your Software Regularly
Outdated encryption software can contain vulnerabilities. Always install updates to stay protected against emerging threats.
Avoid Storing Encrypted Files on Public Devices
Public computers or unsecured Wi-Fi networks can expose your data. Stick to private networks and trusted cloud encryption services like SendMega.
Backup Your Encrypted Files Safely
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
The Role of Encryption in Secure File Sharing
In today’s collaborative digital environment, teams and individuals share files across devices, countries, and networks. But file sharing without encryption exposes sensitive information to potential threats.
This is where encrypted file sharing becomes essential. Platforms like SendMega, Google Drive, and Mega.io use end-to-end encryption and zero-knowledge storage, ensuring that only the sender and intended recipient can access the data.
Whether you’re transferring confidential business documents or sharing personal media, encrypted cloud storage ensures:
-
Data integrity (no unauthorized changes)
-
Confidentiality (no one else can view it)
-
Accessibility (available anywhere, anytime)
Emerging Trends and the Future of Encryption
The future of encryption is exciting—and challenging. As quantum computing and AI-driven cybersecurity evolve, so will encryption technologies.
Post-Quantum Encryption:
Quantum computers could eventually break today’s strongest encryption. Researchers are already developing post-quantum encryption methods that can resist these advanced attacks.
Homomorphic Encryption:
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Security Risks to Watch For
Even with strong encryption in place, certain vulnerabilities can still compromise data security.
Being aware of these risks is essential for maintaining a strong defense.
-
Weak Passwords
Passwords that are easy to guess or crack can undermine even the strongest encryption.
-
Phishing Attacks
Attackers may trick users into revealing encryption keys or login credentials.
-
Poor Encryption Management
Reusing outdated algorithms or failing to rotate keys weakens overall security.
-
Human Error
Storing passwords in plain text or misconfiguring systems can expose sensitive data.
Combating these threats requires awareness, strong cybersecurity practices, and reliable tools. Choosing a trusted service like SendMega helps reduce these vulnerabilities by combining encryption with secure infrastructure and privacy-focused design.
Final Thoughts
Encryption is not just a technical process—it’s a mindset. In a world where data breaches and cyber threats are ever-present, knowing how encryption keeps your files safe online empowers you to protect what matters most.
From understanding how to encrypt your data to using secure encrypted email and cloud encryption security, every step contributes to a safer digital environment. SendMega, Google Drive, mega.io, and other similar platforms bring that protection to your everyday workflow—combining encryption, privacy, and ease of use.
In the end, the key to secure online life isn’t just encryption—it’s awareness, consistency, and trusted technology. Protect your data, choose encrypted solutions, and take charge of your digital world.
Outdated encryption software can contain vulnerabilities. Always install updates to stay protected against emerging threats.
Avoid Storing Encrypted Files on Public Devices
Public computers or unsecured Wi-Fi networks can expose your data. Stick to private networks and trusted cloud encryption services like SendMega.
Backup Your Encrypted Files Safely
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
Public computers or unsecured Wi-Fi networks can expose your data. Stick to private networks and trusted cloud encryption services like SendMega.
Backup Your Encrypted Files Safely
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
Store a copy of your encrypted files on a secure, encrypted cloud or an offline device to prevent data loss.
Be Wary of Phishing Attacks
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
Cybercriminals often target users rather than encryption algorithms. Never share passwords or keys through unverified sources.
The Role of Encryption in Secure File Sharing
In today’s collaborative digital environment, teams and individuals share files across devices, countries, and networks. But file sharing without encryption exposes sensitive information to potential threats.
This is where encrypted file sharing becomes essential. Platforms like SendMega, Google Drive, and Mega.io use end-to-end encryption and zero-knowledge storage, ensuring that only the sender and intended recipient can access the data.
Whether you’re transferring confidential business documents or sharing personal media, encrypted cloud storage ensures:
- Data integrity (no unauthorized changes)
- Confidentiality (no one else can view it)
- Accessibility (available anywhere, anytime)
Emerging Trends and the Future of Encryption
The future of encryption is exciting—and challenging. As quantum computing and AI-driven cybersecurity evolve, so will encryption technologies.
Post-Quantum Encryption:
Quantum computers could eventually break today’s strongest encryption. Researchers are already developing post-quantum encryption methods that can resist these advanced attacks.
Homomorphic Encryption:
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Quantum computers could eventually break today’s strongest encryption. Researchers are already developing post-quantum encryption methods that can resist these advanced attacks.
Homomorphic Encryption:
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
This allows data to be processed without being decrypted—a breakthrough for industries needing privacy-preserving computation, like healthcare and finance.
Blockchain and Decentralized Security:
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Blockchain’s transparent yet encrypted design could reshape how data is stored and validated across distributed networks.
Security Risks to Watch For
Even with strong encryption in place, certain vulnerabilities can still compromise data security. Being aware of these risks is essential for maintaining a strong defense.
-
Weak Passwords
Passwords that are easy to guess or crack can undermine even the strongest encryption.
-
Phishing Attacks
Attackers may trick users into revealing encryption keys or login credentials.
-
Poor Encryption Management
Reusing outdated algorithms or failing to rotate keys weakens overall security.
-
Human Error
Storing passwords in plain text or misconfiguring systems can expose sensitive data.
Combating these threats requires awareness, strong cybersecurity practices, and reliable tools. Choosing a trusted service like SendMega helps reduce these vulnerabilities by combining encryption with secure infrastructure and privacy-focused design.
Final Thoughts
Encryption is not just a technical process—it’s a mindset. In a world where data breaches and cyber threats are ever-present, knowing how encryption keeps your files safe online empowers you to protect what matters most.
From understanding how to encrypt your data to using secure encrypted email and cloud encryption security, every step contributes to a safer digital environment. SendMega, Google Drive, mega.io, and other similar platforms bring that protection to your everyday workflow—combining encryption, privacy, and ease of use.
In the end, the key to secure online life isn’t just encryption—it’s awareness, consistency, and trusted technology. Protect your data, choose encrypted solutions, and take charge of your digital world.
Recent Posts
All Categories
- Cloud Storage (4)
- File Share (4)
- Guides (2)
- News (2)
- Online Meetings (2)






